When it comes to DNS errors triggered during web monitoring, it is not typically easy to quickly identify and understand the exact issue that leads to connection errors. There is a lot that goes on behind the scenes (in just a matter of seconds) that we take for granted. So, when DNS issues occur, the impacts may be felt immediately across a wide variety of resources and internal and external users. Websites experiencing DNS errors may result in user experience issues, leading to discouraged users and loss of revenue for the business. Even more, if DNS configurations are improperly set, or issues go unchecked, it can lead to a loss of domain authority.
In this article, we will walk you through some DNS error troubleshooting steps.
For common recommendations on troubleshooting errors, please visit the Troubleshooting Monitoring Errors article.
-
What is DNS and How Does it Work?
Why Do DNS Errors Occur?
In general, the most common reasons for DNS errors, like DNS timeouts or DNS misconfigurations, occurs with the DNS service provider and the impact to users can vary depending on the severity of the error. The DNS is a vast and complex network. Some issues may be hardware related and can be resolved quickly, but some errors may require more in-depth DNS troubleshooting, resulting in additional resources and time to fix.
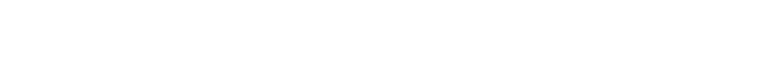
For example, DNS tree propagation can be considerably long. The DNS chain to the authoritative DNS nameserver where the IP address of the host is stored is long, which increases the DNS resolution time. In this case, the DNS timeout error can be received due to inconsistency between a monitoring timeout limit and time it takes to complete DNS resolving.
If DNS resolving takes more than 11 seconds (allowed by default), the DNS timeout error will be generated. Note that this is not necessarily a website availability issue, but a long timeout that was terminated.
DNS Troubleshooting Tips & Best Practices
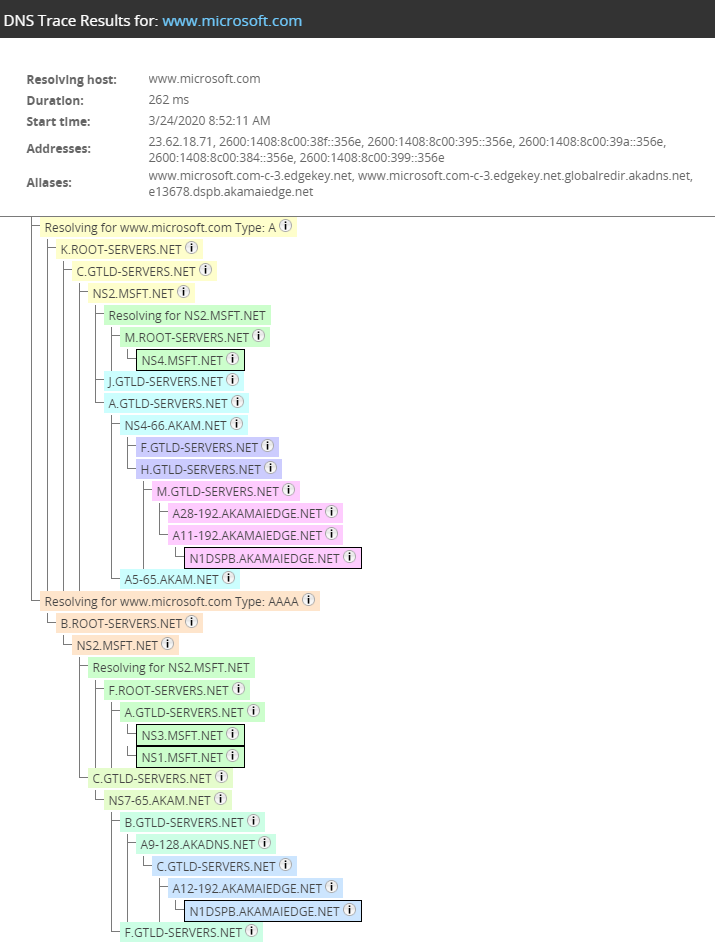
One of the first troubleshooting steps we recommend is checking the DNS tree and understand at which point a DNS server issue or timeout occurred. We recommend pulling an Online Report for the monitoring device, and on the Log tab, use the built-in DNS Trace option.
To build a DNS tree in real-time, use the Dotcom-Monitor DNS trace tool. On the DNS Trace tab, enter the IP and location and start the test. The propagation is started from the root servers as it is executed for the Device Cached or Non-Cached DNS modes.
Troubleshooting DNS Errors
To troubleshoot a DNS error, review the error description provided for each server node of the DNS tree as shown in the picture above (step 2).
If you experience DNS errors often, you can set up a separate DNS task for the domain in question (the Verify Response On option set to First Responding) and set up a specific monitoring frequency to check the domain name resolution into an IP.
Other areas to investigate when troubleshooting DNS errors include network devices, browsers and/or devices, DNS records, service provider, and latency issues. It is good practice to have a checklist of items to troubleshoot. Like troubleshooting anything, it is best to start with the item(s) that are easiest to review and check and then move down the list to the more difficult and time-consuming items, such as troubleshooting misconfigured DNS records or reviewing latency issues.
-
DNS Response and Error Codes
Troubleshooting DNS Timeout
If a DNS server timeout is the issue, we recommended to contact your provider to check if any DNS servers on their side have performance degradation. Also, an overloaded DNS server can slow down the server response time to a name request.
If there are no DNS server performance issues, use one of the suggested approaches:
- Change the DNS resolve mode to TTL Cached.
- Use an External DNS Server.
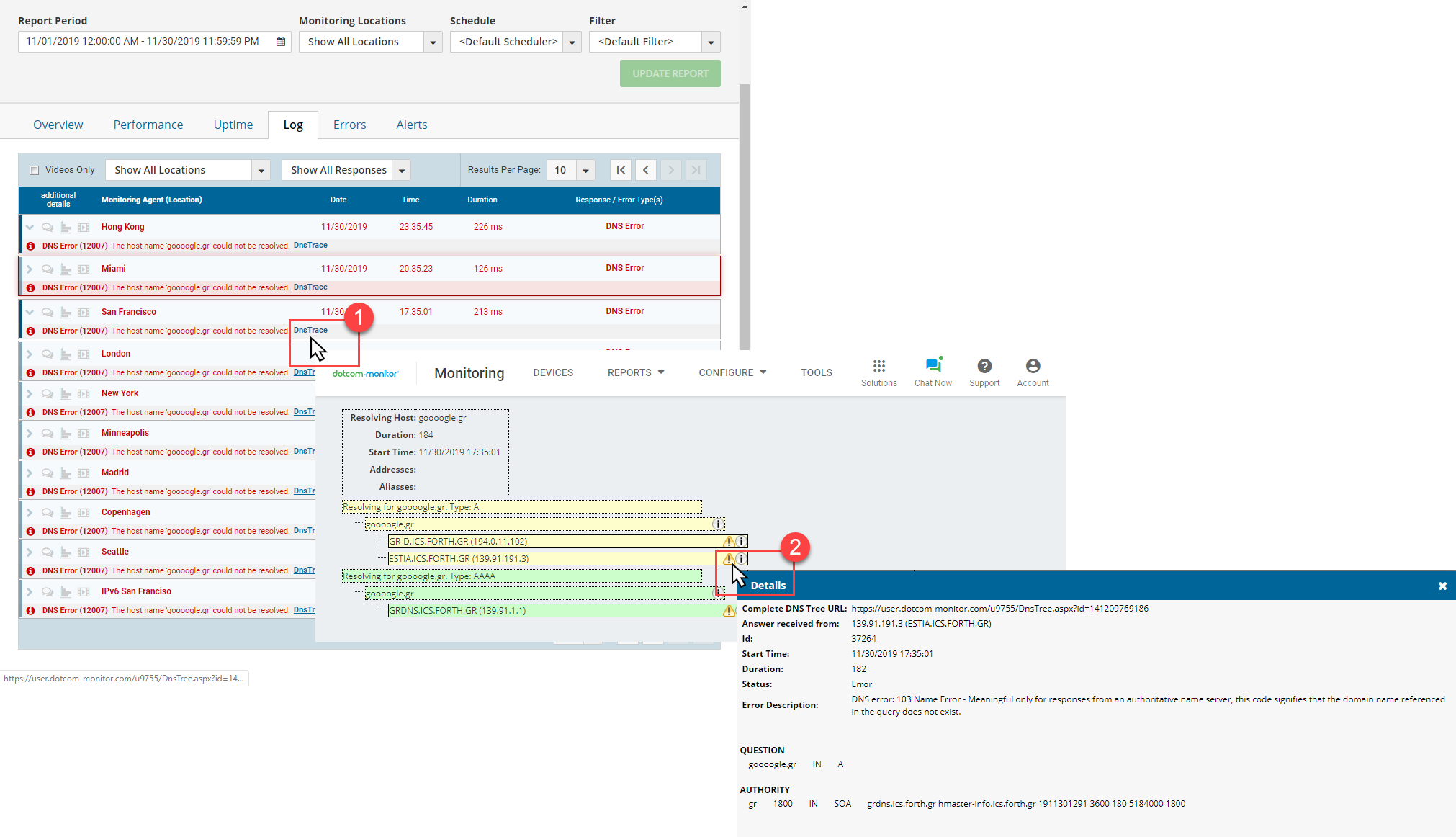
To deal with DNS timeout errors, you can change the resolving mode from Device Сached to TTL Сached.
By default, in the Device Cached mode, Dotcom-Monitor makes a full resolution from root DNS servers without any caching on every check. In other words, this is the most reliable approach because the entire DNS chain, starting from the root DNS server, is checked. However, the disadvantage of this approach is that it increases device execution time and in the case of a long DNS tree, can lead to timeout issues.
On the other hand, the TTL Cached mode allows for mimicking a DNS lookup as it is executed on an actual user’s computer. To resolve a website IP address, the DNS lookup information is cached locally on a user’s computer. On the first request for a domain’s IP address, the DNS record is saved to the cache and used on subsequent requests to the domain, which helps to speed up the process by skipping all the lookup steps from the DNS resolution process, better for the overall user experience.
Similarly, a local DNS server with an installed monitoring agent is used to pre-cache lookup information in the TTL Cached mode. The DNS records are saved in the local server’s cache during TTL. Depending on what the TTL is for a specific host (usually around a day), it will rarely be requested. Therefore, the possibility of getting a timeout is reduced significantly.
To use a public caching service, such as Google (8.8.8.8, 8.8.4.4) or Cloudflare (1.1.1.1), change the DNS mode to External DNS Server. Dotcom-Monitor will fetch IP addresses from a public service’s DNS cache. This option will reduce DNS resolving time and can help to troubleshoot a timeout issue.
DNS Resource Records
DNS resource records (RRS) are essentially what hold the information to everything related to your domain. Simply put, DNS records help point users in the right direction to anything related to your domain. For example, DNS records are important for directing emails to the right email server or the right domain to the right web server, and so on. There are well over 40 different types of resource records (and many more that have been retired) that cover a wide array of categories and different functions, such as mail records and website records to information records. We will cover the all the DNS resource record types supported by the Dotcom-Monitor platform.
-
Dotcom-Monitor Supported DNS Resource Record Types
The Importance of DNS Monitoring
Setting up and configuring DNS monitoring is important for many reasons, but the primary reason is to ensure that any network and website outages or slow response times are kept to a minimum and don’t impact the user experience. And more importantly, when they do happen, they can be identified quickly to prevent more users from being affected. Users that can’t access your websites are going to be frustrated and quickly go elsewhere to find what they were looking for. You want to be sure to you and your teams are notified immediately if something goes wrong so you can begin working on a fix as quickly as possible. DNS monitoring is also important for the following factors:
Meeting Service Level Agreements
Not only is DNS monitoring good for catching configuration issues, but DNS monitoring can also be utilized to ensure SLAs are being met by your service providers. DNS monitoring is also critical for ensuring SLAs are being met and uptime is within the agreed upon thresholds. If not, DNS monitoring can show you where the issues lie and provide you with the information to start the process of resolving the problem. In some cases, it could be a third-party service that you have no control over.
DNS Hijacking
DNS hijacking also referred to as DNS poisoning or DNS spoofing, refers to the process of changing DNS cache so that it points to a different website for malicious purposes. Attackers can impersonate the authoritative nameservers and respond with fake information back to the user where the attackers can point unsuspecting users to fake sites.
DDoS Attacks
DDoS attacks are an attempt to bring down a website by flooding a server, service, website, or network with traffic. There are several types of DDoS attacks that can affect different components, but a DDoS attack to the DNS server is called a DNS amplification. Essentially, what occurs is that an attacker creates a request for not just a domain, but everything related to that domain, and repeats that with multiple queries and multiple open DNS resolvers. DNS monitoring ensures that if any tampering with your DNS records or configuration issues are occurring, alerts are sent to the appropriate teams so they can be dealt with immediately, helping to protect your company from potential risks or loss of revenue and users.
Building and Maintaining Customer Trust
Trust is a major factor in why customers choose one product or service over another. If your website is experiencing issues, whether it is an issue you even have control over or not, customers may view that as a reflection of your products or services. Their view will be that your site is unreliable, so how can they trust that your products or services are any different.
Monitoring DNS Performance: Good for Business and the Bottom Line
Although DNS far to often gets overlooked and taken for granted, it is a critical and essential piece for customers and businesses alike, which is why DNS monitoring is so important for any business that has an online presence. With DNS monitoring from Dotcom-Monitor, you can monitor DNS availability and health 24/7 from those locations around the world where your customers reside and get alerted to any errors that occur along the DNS tree.