ADFS (Active Directory Federation Services) is a solution from Microsoft for single sign-on (SSO) functionality. It is used by organizations that have their users on Windows Servers to provide authentication and authorization to web-based applications or services outside the organization. ADFS implements federated identity and claim-based access control to authenticate and authorize users, thus maintaining security. Claims-based authentication is way to provide access to users based on set of claims which contain the information about the identity contained in tokens.
The inner workings of ADFS can be understood by a simple example. Assume a company ‘A’ which hosts ADFS on their servers, has access to a user’s credentials. It is configured to provide trust to other applications ‘B’ and ‘C’ that require access tokens from the ADFS for authentication. When a user tries to access application ‘B’ from the browser, it redirects user to a proxy server of application ‘A’ where the user is asked to log in. After the user enters their valid username/password, the access token is generated for that user and redirected to the application ‘B’ along with the token. The same process occurs when the user wants to access application ‘C.’
Why Azure ADFS?
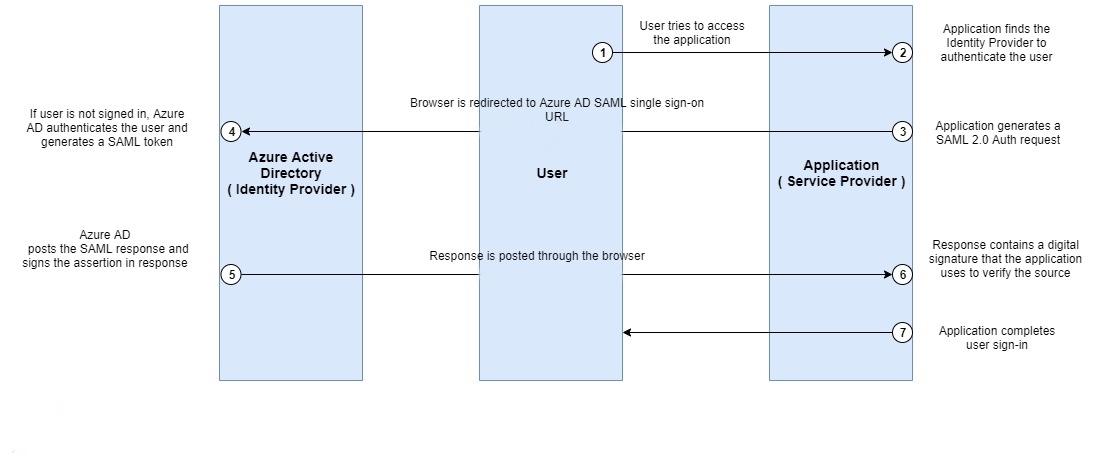
Azure ADFS allows organizations to streamline access to their applications by providing SSO capabilities for users across different domains. This setup not only simplifies user authentication but also enhances security by minimizing the need for multiple passwords. Azure ADFS works seamlessly with a wide array of Microsoft services, as well as third-party applications, making it a flexible and scalable solution for organizations of all sizes. Another advantage is that it integrates smoothly with Azure Active Directory, providing advanced security features like conditional access, multi-factor authentication, and support for various authentication protocols, such as SAML, WS-Federation, and OAuth. In short, Azure ADFS empowers businesses to provide a unified, secure, and convenient login experience, making it an excellent choice for managing user identities across cloud and on-premises environments.
For organizations using Azure ADFS as the gateway to Microsoft 365 services, our guide on Office 365 synthetic monitoring and Azure AD covers how to layer identity monitoring on top of M365 availability checks for complete visibility.
Issues faced by Applications using Azure ADFS
Despite its advantages, applications relying on Azure ADFS can face various issues that disrupt service or hinder the user experience. One common issue is authentication delays or failures, often caused by configuration issues or network connectivity problems between ADFS and the identity provider. Outages or service interruptions can prevent users from logging into critical applications, causing productivity loss and frustration. Security misconfigurations can also pose a threat, as weak configurations might expose applications to unauthorized access or data breaches. Furthermore, ADFS token expiration and renewal failures can cause unexpected session timeouts, resulting in disruptions to user workflows. Finally, ADFS integration with third-party applications can be complex, with compatibility and configuration challenges that affect authentication reliability. For organizations that rely heavily on ADFS, addressing these issues proactively is essential to maintaining security, availability, and user satisfaction.
Many of these failure modes apply equally to Okta-federated applications — our guide on monitoring applications that use Okta authentication explains the SAML assertion quirk that makes standard monitoring blind to service-side failures even when auth technically succeeds.
Why Monitor Applications that use ADFS?
Monitoring applications that depend on Azure ADFS is essential for several reasons. First, regular monitoring helps detect authentication issues early, ensuring users can log in without interruptions and preserving productivity. Monitoring also enhances security by allowing organizations to spot suspicious login patterns or abnormal access attempts, which may signal security threats like brute-force attacks or unauthorized access. Additionally, effective monitoring can help identify configuration issues and optimize performance by tracking metrics such as response times and token issuance delays, allowing for faster troubleshooting. By proactively addressing these issues, organizations can prevent the frustration and potential downtime caused by authentication failures. Ultimately, monitoring applications using ADFS ensures that user access remains smooth, secure, and reliable, which is especially critical for applications that handle sensitive or business-critical data.
How Can we Monitor Applications that use Azure ADFS?
To ensure seamless authentication and access, implementing synthetic monitoring for applications using Azure ADFS is highly effective. Synthetic monitoring uses scripted, simulated user interactions to check the performance and availability of your applications in real-time. By simulating login attempts through ADFS, synthetic monitoring can proactively detect issues such as login delays, token errors, and outages, ensuring users experience a reliable and responsive system.
Dotcom-Monitor is an ideal choice for synthetic monitoring of ADFS-dependent applications. With Dotcom-Monitor’s capabilities, you can set up synthetic transactions that simulate ADFS authentication processes, ensuring your login and authentication flows work seamlessly at all times. Dotcom-Monitor offers real-time alerts for any issues detected during the synthetic checks, allowing IT teams to address problems proactively before users are impacted. Additionally, Dotcom-Monitor provides detailed reports on response times, error rates, and availability, making it easier to analyze performance trends and optimize the authentication process.
With Dotcom-Monitor’s synthetic monitoring, you can also schedule regular checks to ensure that tokens are issued correctly, SSL certificates are valid, and any third-party integrations continue to function smoothly with ADFS. This automated approach minimizes manual effort and allows you to monitor your applications 24/7, ensuring the authentication process remains secure and efficient. Dotcom-Monitor’s user-friendly interface and customizable alerts make it a powerful tool for monitoring ADFS applications, helping organizations maintain optimal performance and security.
Synthetic Monitoring from Dotcom-Monitor
Dotcom-Monitor provides various solutions and features to help user monitor their most critical websites and applications. Features like the EveryStep Web Recorder, configurable alerts, real-time reports, and third-party integrations, and more, gives users the tools and information they need to ensure their applications are working smoothly.
- Quick Solutions for Performance Problems: By using the EveryStep Web Recorder, web application performance issues can be detected quickly. For applications that use ADFS, this tool can record scripts for user steps when a user tries to log in using SSO, or the screen where OAuth token is sent by ADFS, and use it to monitor the web applications. Once the recorded scripts are ready and uploaded into the platform, you can set different thresholds for which to receive alerts. Detailed report on the problem can be created with screenshots and videos of the error, like if the user authentication service is failing etc., which can help the organization act quickly on repairing the issue before other users face the same issue.
- Alerts: You can create and configure custom notification groups with different types of alert mechanisms. Details can be checked and verified. If something goes wrong, it can identify the error and send alerts to the necessary people or teams to notify them of the problem. Alerts can be sent if the application goes down or if users fail to authenticate repeatedly. By proactively monitoring your applications, you ensure that the impact to users is minimal.
- Reporting: Gaining visibility and knowledge on user actions. Various types of reports can be generated by the platform, giving a wealth of performance data, such as downtime/uptime percentages, response time standard deviation, average response times, successes/failures, and more.
- Validating SLAs: Along with performance dashboards and alerts, the platform can also provide reporting to validate SLAs by IAM systems. For example, different IAMs claim their SLAs to be outstanding, but how can the organizations just simply trust that without verifying? The simple answer is that Dotcom-Monitor can do that for the organizations by creating detailed SLA reports to show the exact availability percentage of IAM systems. Dotcom-Monitor is set up to monitor and report on the commitments service providers make to customers in their SLAs.
Explore the full capability set for Azure and Microsoft environments on our SaaS monitoring platform for Azure and Microsoft environments page — including private agent options for on-premises ADFS deployments.
In Conclusion: Monitoring Applications that use Azure ADFS
Azure ADFS provides a robust and flexible solution for managing user access across multiple applications, but it is not without its challenges. From configuration issues to performance lags, applications that rely on ADFS can experience disruptions that impact both productivity and user satisfaction. Monitoring these applications is essential to catching potential issues early, ensuring secure and consistent access for users. Synthetic monitoring, especially with Dotcom-Monitor, offers a proactive approach to maintaining the health and reliability of ADFS-dependent applications. By simulating real-world interactions and monitoring for anomalies, Dotcom-Monitor helps organizations detect issues, optimize performance, and deliver a seamless user experience. In today’s fast-paced digital environment, monitoring ADFS applications isn’t just beneficial, it’s essential.
The choice between cloud-based and on-premises monitoring tools has direct implications for ADFS coverage — our comparison of cloud-based vs on-premises monitoring explains where each model excels and when hybrid deployment is the right answer.

