An expired or misconfigured SSL/TLS certificate doesn’t fail quietly. Users get blocked by browser warnings, conversions drop, and teams scramble to diagnose whether the problem is expiration, a missing intermediate, an SNI/hostname mismatch, or a CDN edge serving an old chain. That’s why SSL certificate monitoring in 2026 is less about “check the expiry date” and more about continuous validation + fast alerting + enough context to fix the issue quickly.
An expired or misconfigured SSL/TLS certificate doesn’t fail quietly. Users get blocked by browser warnings, conversions drop, and teams scramble to diagnose whether the problem is expiration, a missing intermediate, an SNI/hostname mismatch, or a CDN edge serving an old chain. That’s why SSL certificate monitoring in 2026 is less about “check the expiry date” and more about continuous validation + fast alerting + enough context to fix the issue quickly.
This guide compares the 12 best SSL certificate monitoring tools in 2026, focusing on what each tool does, what it’s like to use, where it fits, and what the tradeoffs are. (Pros and cons are bullets only; everything else is text.)
What is SSL Certificate Monitoring?
SSL certificate monitoring is the practice of continuously checking your SSL/TLS certificates for expiration dates, configuration errors, chain problems, and unexpected changes. Unlike one-time certificate checkers, monitoring tools run scheduled validations from multiple global locations and alert your team before issues affect users.
What to look for in an SSL certificate monitoring tool
Most top-ranking comparison articles converge on a few evaluation points:
- Proactive expiry alerts (multiple reminder windows like 30/14/7/1 days)
- Validation that matches real-world failures (invalid certs, chain issues, wrong cert served, etc.)
- Multi-location checks (especially important with CDNs and geo routing)
- Actionable alerting (email + chat + escalation options)
- History and reporting (audits, client reporting, post-incident review)
- Fits your workflow (uptime-first tools vs synthetic-first tools vs cert-dedicated tools)
Quick comparison table
For a quick fit by use case:
- Best for enterprises: Datadog
- Best for small teams: UptimeRobot
- Best for certificate governance: TrackSSL
- Best for global monitoring: Dotcom-Monitor
- Best for incident workflows: Better Stack
| Tool | What it’s strongest at | SSL monitoring focus | Reporting/history | “Feels like” |
| Dotcom-Monitor | Global checks + audit-ready reporting | SSL + website/transaction monitoring | Strong | Monitoring platform |
| Better Stack | Uptime + incident workflow | SSL inside uptime/keyword monitors | Good | Incident-driven uptime |
| Sematext Synthetics | Deep synthetic SSL validation | Chain-aware checks + diagnostics | Strong | Engineering-focused synthetics |
| Datadog Synthetics | Enterprise observability + SSL tests | SSL tests integrated into Synthetics | Strong | Observability suite |
| Site24x7 | Suite monitoring + SNI environments | SNI + revocation/CA checks | Strong | IT ops suite |
| UptimeRobot | Fast setup + common SSL errors | Expiry + SSL error alerts | Basic–Good | Simple uptime tool |
| StatusCake | Straightforward SSL checks | Expiry alerts + visibility | Good | Uptime vendor |
| Pingdom | SSL embedded in HTTPS uptime checks | Cert errors + expiry in uptime | Good | Set-and-forget uptime |
| UpDown | Minimalist + predictable reminders | Expiry reminders + webhooks | Basic–Good | Developer-friendly |
| TrackSSL | Dedicated cert monitoring | Expiry + certificate change alerts | Good | Certificate-focused tool |
| Oh Dear | Cert change detection + clean notifications | Expiry + certificate change monitoring | Good | Developer-friendly monitoring |
| Cert Spotter (SSLMate) | Certificate Transparency monitoring | CT issuance alerts + expiry/invalid cert signals | Good | Security-focused CT monitor |
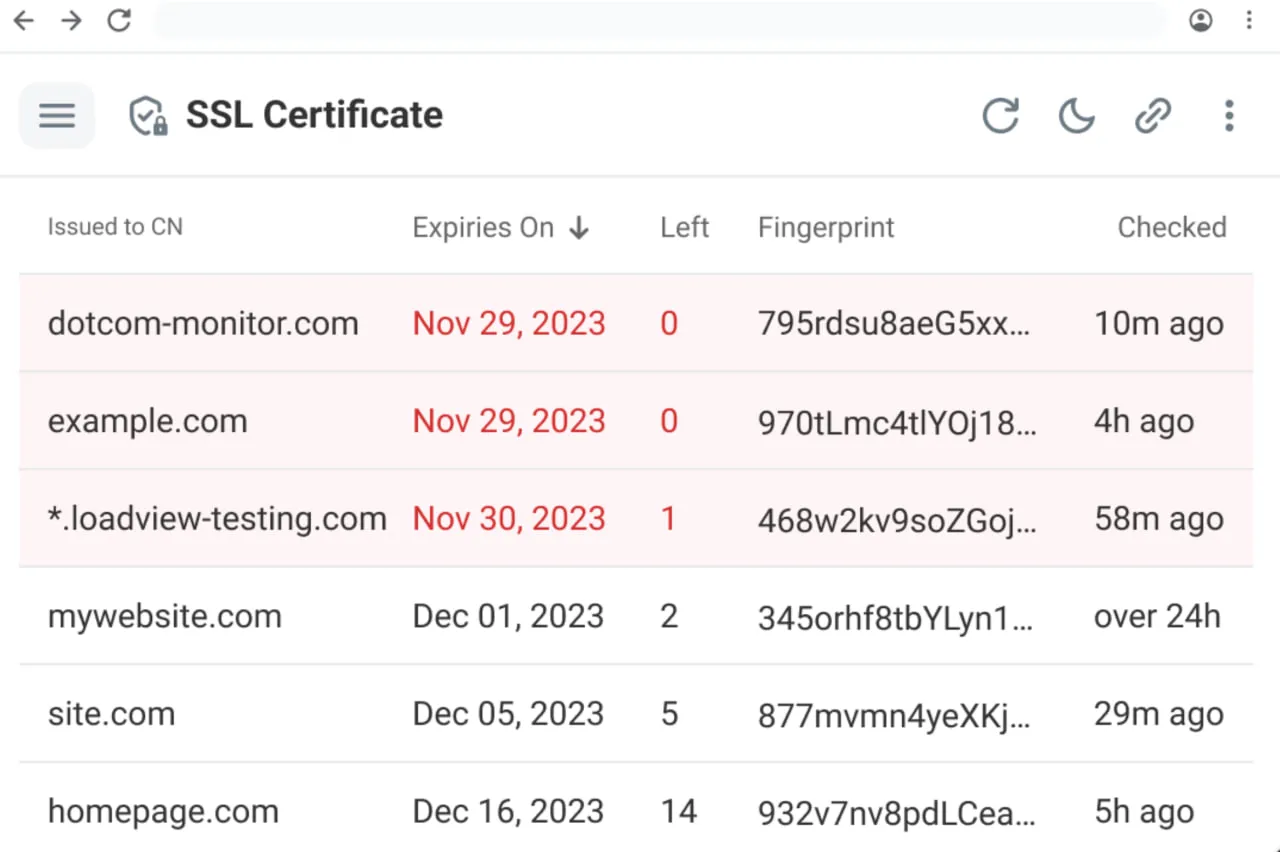
1. Dotcom-Monitor
Dotcom-Monitor positions itself as an “intelligent SSL certificate checker” that runs regular certificate checks from multiple locations, so you can see SSL status the same way users do globally. That multi-location approach matters in 2026 because certificate problems often appear only in certain regions – especially when a CDN or edge node serves an old certificate chain. Dotcom-Monitor also fits SSL monitoring into a broader reliability workflow: you’re not only validating the certificate, you’re validating the website and critical user flows that depend on it, which is typically how certificate issues show up in production.
Another differentiator is the platform’s emphasis on visibility and accountability: when you need to show stakeholders that SSL was valid across locations over time (or prove renewal happened), reporting and history become a real feature – not a “nice to have.” Dotcom-Monitor also advertises a global monitoring network (nearly 30 locations) that supports this approach. Finally, if your certificate management process is split across teams (web, infra, security), Dotcom-Monitor’s alert routing helps turn “someone should renew this” into an owned operational task.
Pros
- Multi-location checks help catch CDN/edge inconsistencies early
- SSL monitoring fits naturally with uptime and synthetic/transaction monitoring
- Strong reporting/history for audits, stakeholders, and client reporting
- Works well for portfolios of sites and endpoints
Cons
- More platform than you need if you only want a basic expiry reminder
- Most valuable when used alongside other monitoring modules, not just SSL
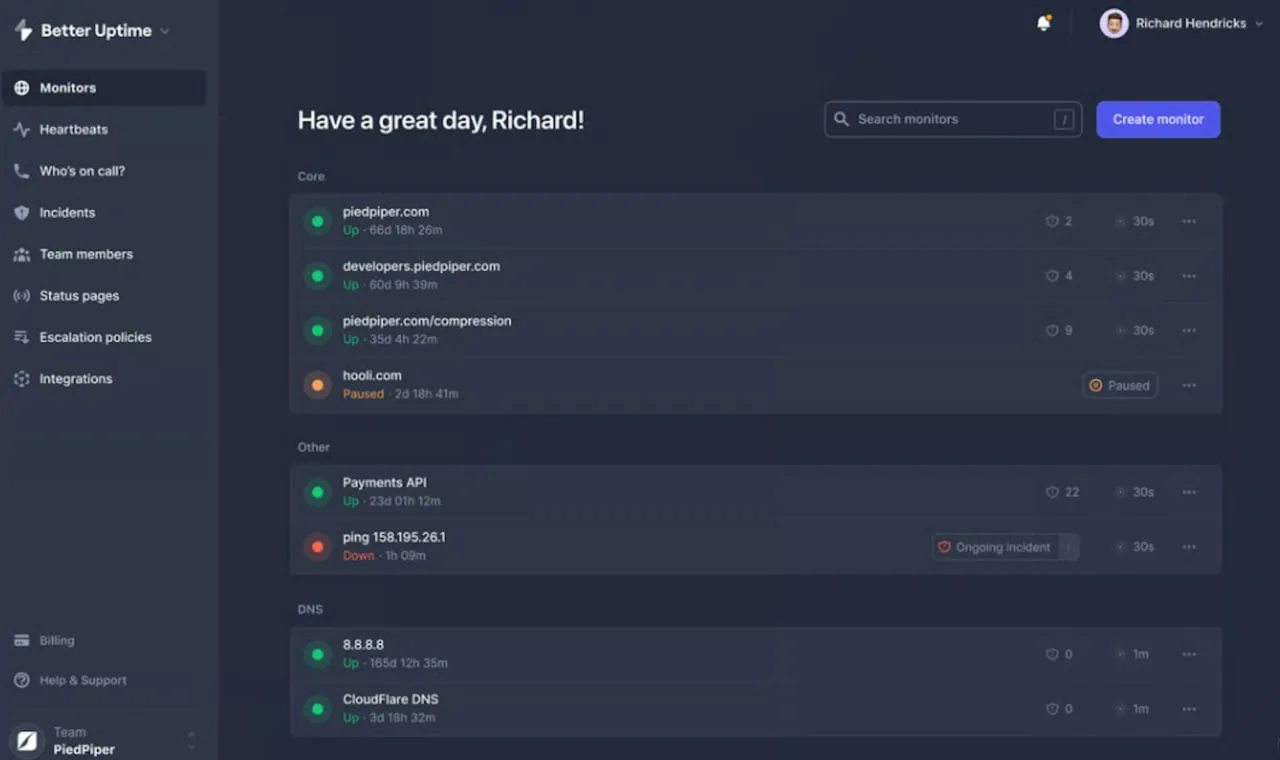
2. Better Stack
Better Stack’s SSL approach is operational: SSL certificate monitoring is built into uptime monitors and keyword monitors, so TLS failures are treated like availability issues and routed into your incident process. In practice, that’s often the right model – because when TLS breaks, it becomes a “site down” problem from the user’s perspective. Better Stack lets you enable certificate checks (including validity and expiration tracking) from a monitor’s advanced settings.
Where Better Stack tends to shine (and why it’s common in top comparisons) is the workflow after detection: alert routing, collaboration, and incident handling. Instead of certificate alerts going to a forgotten inbox, they show up where teams actually respond. This is a solid fit when you want SSL issues to follow the same escalation rules as downtime.
Pros
- SSL checks are integrated directly into uptime/keyword monitors
- Strong incident workflow: certificate issues become actionable quickly
- Simple configuration (turn on SSL/TLS verification per monitor)
Cons
- Less oriented toward certificate lifecycle governance (inventory/ownership/change control)
- Certificate-focused diagnostics aren’t as central as in synthetic-first tools
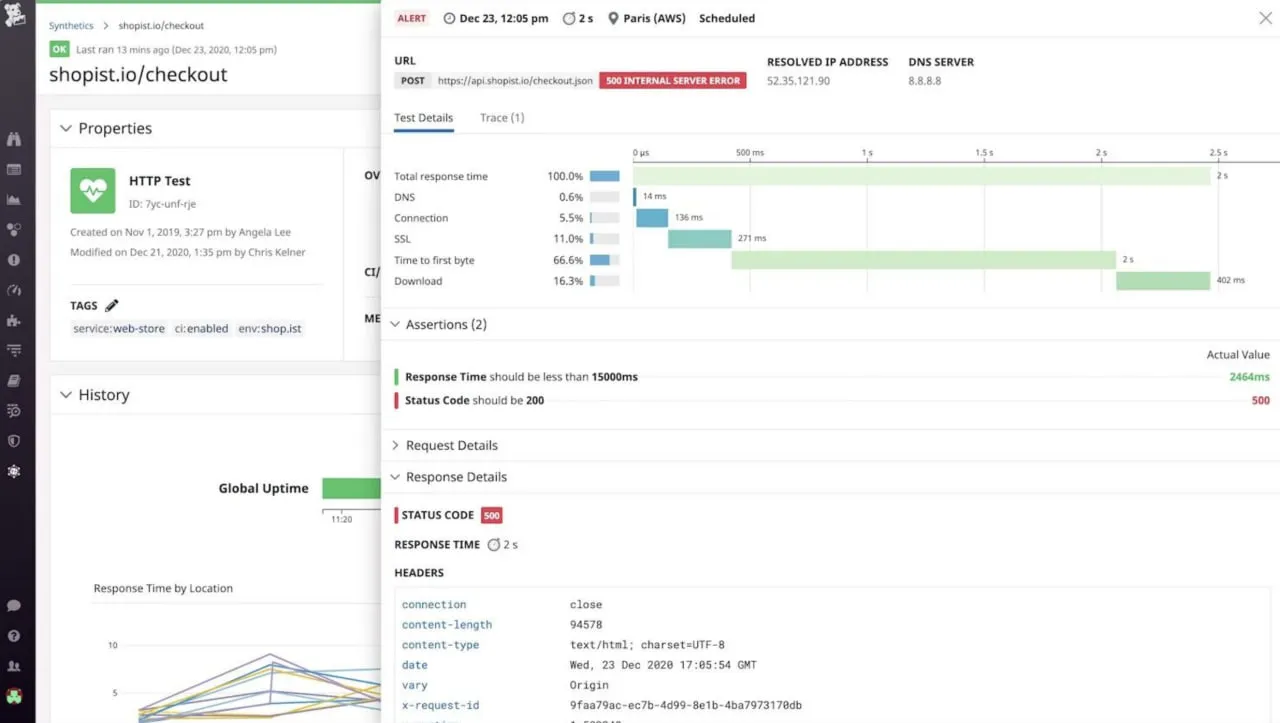
3. Sematext Synthetics
Sematext is a synthetic monitoring platform that explicitly performs SSL certificate checks across the entire certificate chain (leaf, intermediate, and root), rather than only checking the end-entity certificate. This matters because real outages often come from chain problems (expired intermediate, missing intermediate, incorrect chain order), and those can be difficult to diagnose if your tool only reports “SSL handshake failed.” Sematext also supports structured SSL alerting windows (for example, days-before-expiry alerts) and can generate alerts when a certificate change is detected.
Day to day, Sematext tends to appeal to engineering teams because the synthetic monitoring context gives you better debugging breadcrumbs: what endpoint failed, what changed, and when it started failing. If you already run synthetic HTTP/browser checks for SLAs, adding SSL validations is a low-friction way to expand coverage without introducing a separate system.
Pros
- Chain-aware monitoring reduces “surprise intermediate/root expiry” incidents
- Strong diagnostics when paired with synthetic HTTP/browser checks
- Can alert on expiry windows and detected certificate changes
Cons
- For Browser/User Journey scripts, Sematext notes SSL checks are performed for the first page only (an important limitation)
- Overkill if your only requirement is a renewal reminder
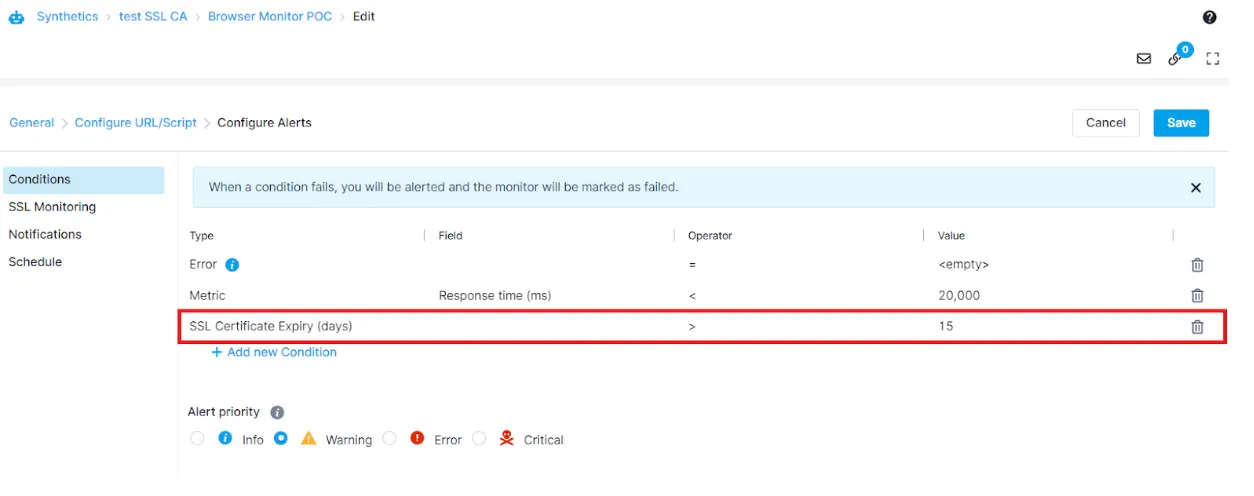
4. Datadog Synthetics (SSL tests)
Datadog’s SSL tests are designed for proactive monitoring of certificate validity and expiration, with alerts that include failure details to help pinpoint root cause. For teams already using Datadog, the big advantage is consolidation: SSL health becomes one more standard signal alongside metrics, logs, traces, and synthetic uptime. In large organizations, that consistency matters – certificate issues across internal services can be treated the same way as other reliability regressions.
Datadog also frames Synthetics as multi-layer monitoring across network-level (including SSL, DNS, and more), which makes it easier to operationalize certificate checks as part of a broader testing program rather than a one-off reminder tool. If you want SSL checks to inherit your existing tagging, ownership, and incident routing model, Datadog is strong – assuming you’re already invested in the platform.
Pros
- Strong fit if Datadog is already your observability “home”
- SSL tests integrate cleanly with enterprise alerting and incident workflows
- Scales well to many endpoints, including internal services
Cons
- Often too heavy/costly if you’re not already using Datadog
- Not a dedicated certificate governance tool by itself
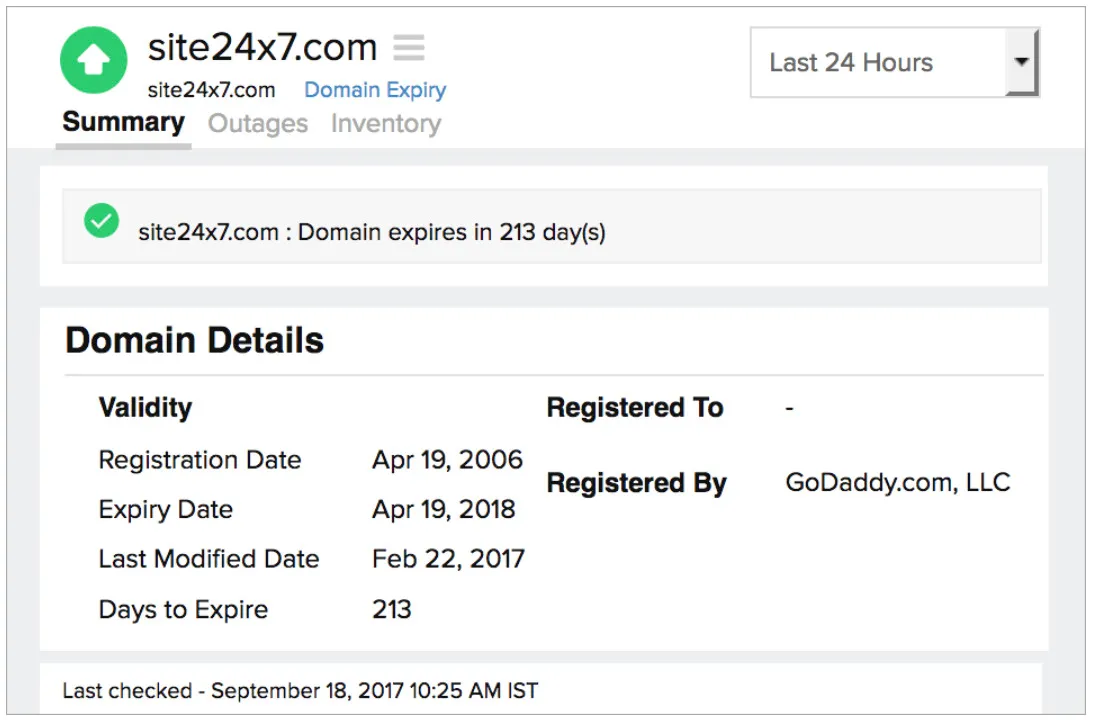
5. Site24x7
Site24x7’s SSL/TLS monitoring is attractive when you deal with real-world hosting complexity, especially SNI (multiple certificates on the same IP). Site24x7 explicitly calls out SNI-enabled servers and the need to retrieve the correct SSL expiry information in those environments. It also captures certificate metadata (CA, owner, issue date, expiry date, days remaining), which is useful for operational visibility.
Beyond expiration, Site24x7 supports checks such as OCSP revocation status and can flag if a CA is blocklisted, which pushes the tool closer to “SSL health and security hygiene,” not just “calendar reminders.” If your SSL monitoring needs to fit inside broader IT operations (servers, networks, applications), Site24x7’s suite approach can be a real advantage.
Pros
- Strong for SNI environments where simpler tools can check the wrong cert
- Includes security-oriented checks like OCSP revocation and blocklisted CA detection
- Works well as part of an IT ops monitoring suite
Cons
- Suite products can feel heavy if you only need SSL monitoring
- More features to configure and maintain than minimalist tools
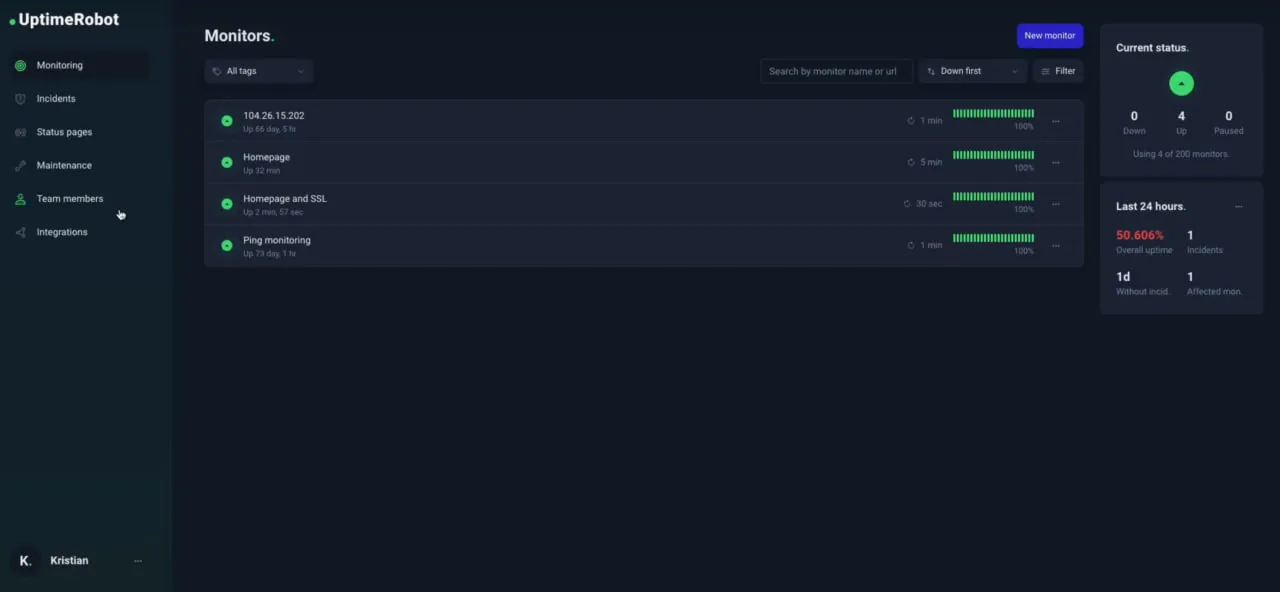
6. UptimeRobot
UptimeRobot is popular because it’s simple: you add an HTTPS monitor and enable SSL monitoring to get notified about certificate errors and upcoming expirations. UptimeRobot’s help docs state that expiration checks run once every 24 hours, with default reminder windows at 30, 14, 7, and 0 days, and you can customize intervals. For many teams, that’s exactly what they need: prevent the most common certificate outage (expiration) with minimal setup.
UptimeRobot also markets SSL monitoring as a built-in part of its monitoring flow – useful when you want a tool non-specialists can understand and act on. It’s often used as the first layer of monitoring, and teams add deeper synthetic/cert tooling later if chain diagnostics or governance becomes important.
Pros
- Very fast setup and easy UI
- Customizable reminder intervals with sensible defaults
- Good “first line of defense” against expiration-related outages
Cons
- Daily checks may be sufficient for expiry risk, but not deep TLS validation
- Limited certificate governance features (inventory/change management/audits)
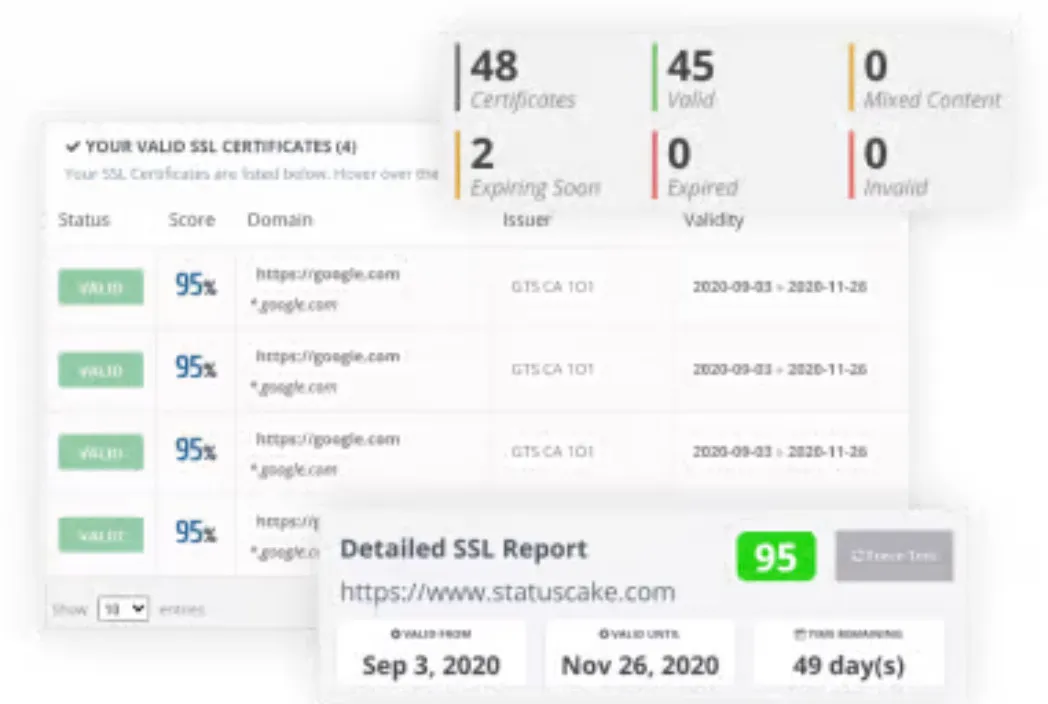
7. StatusCake
StatusCake provides SSL monitoring focused on staying ahead of renewal deadlines and improving visibility into certificate dates. StatusCake states you can see certificate start/end dates and set expiry alerts at 1, 14, and 30 days before expiration. For teams managing multiple marketing sites or standard web properties, this is a clean and practical solution – especially when you also want uptime monitoring from the same vendor.
StatusCake tends to land in the “middle ground” category: more structure than ultra-minimal monitors, but still primarily oriented around uptime-style use cases rather than certificate lifecycle governance. If your main risk is “missed renewal,” StatusCake’s model fits well.
Pros
- Straightforward expiry alerts and certificate date visibility
- Works nicely alongside general website monitoring
- Simple operational model for multi-site owners
Cons
- Less specialized for certificate change detection or advanced TLS diagnostics
- Not designed for deep certificate governance workflows
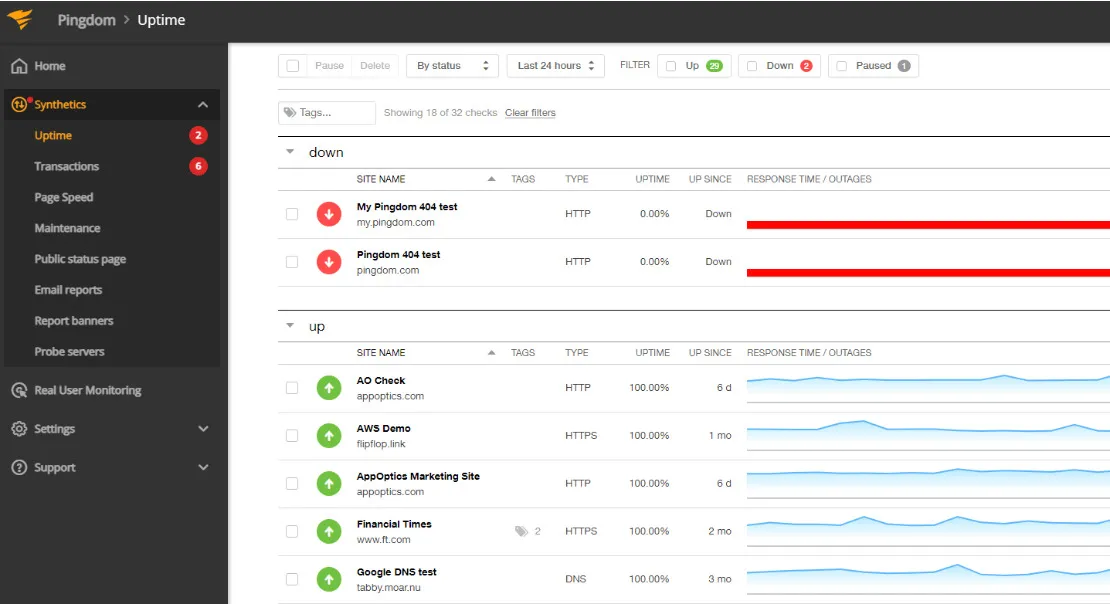
8. Pingdom
Pingdom’s SSL certificate monitoring is essentially enabled by selecting HTTPS when setting up an uptime check. Pingdom states that once an HTTPS check is enabled, it monitors certificate errors automatically and notifies you about certificate problems and upcoming expiration. The SolarWinds Pingdom documentation reinforces this: certificate monitoring is available for HTTPS uptime checks, and the tool monitors for certificate errors automatically.
Operationally, this is the “set-and-forget” approach: certificate failures become uptime failures, so they surface where your team already reacts. This works especially well for straightforward websites where the key requirement is “don’t let TLS break access.”
Pros
- SSL monitoring is integrated into HTTPS uptime checks (simple setup)
- Certificate errors surface as availability issues, which teams prioritize
- Works well for teams already standardizing on Pingdom uptime checks
Cons
- Less certificate-specific visibility than dedicated certificate tools
- Not oriented toward certificate inventory, ownership, or change tracking
9. UpDown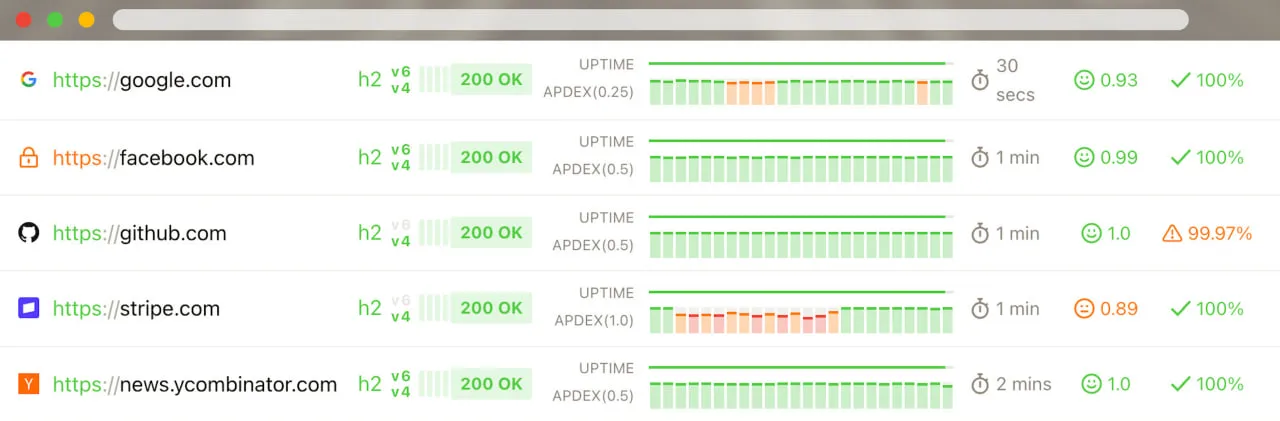
UpDown is a lightweight monitoring service that’s popular with developers because it’s predictable and automation-friendly. UpDown’s SSL expiration notifications are explicitly described as alerts 30, 14, 7, and 1 day before expiry, sent at 10:00 a.m. in your time zone because they’re reminders rather than critical alerts. It also supports webhooks for SSL expiration events, which is useful if you want to automatically open tickets, post to chat, or trigger internal runbooks.
The UpDown model is ideal when renewals are automated but you still want independent verification that automation is working – and you want notifications to be easy to integrate into your existing tools. UpDown also documents integrations/webhook-friendly workflows that make it simple to connect to common incident systems.
Pros
- Predictable reminder cadence that teams can plan around
- Webhooks make it easy to automate tickets/runbooks for renewals
- Minimal overhead for monitoring many endpoints
Cons
- Not a certificate governance platform (ownership, audit reporting, policy)
- Less diagnostic depth than synthetic-first platforms
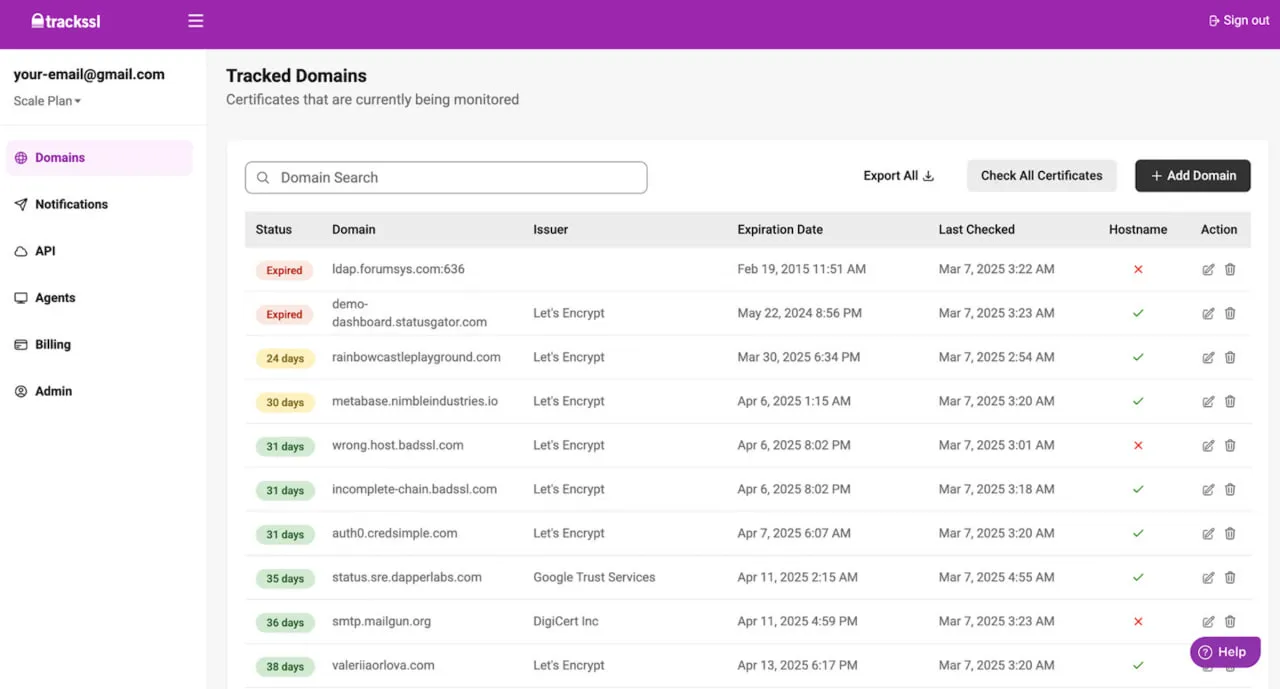
10. TrackSSL
TrackSSL is certificate-focused rather than uptime-focused, which becomes increasingly valuable in 2026 because automated renewal (ACME, CDNs, hosting platforms) introduces a new risk: unexpected certificate changes. TrackSSL emphasizes expiry notifications via multiple channels (email, Slack, SMS, Teams, webhooks) and also highlights “Monitor SSL Changes” and “SSL Certificate Transparency Alerts” as core features.
In practice, TrackSSL is commonly used as the “certificate oversight layer” paired with an uptime monitor: uptime tools tell you when the service is down, while TrackSSL tells you when the certificate changed, when it’s nearing expiry, and when something looks off. If your organization doesn’t fully control issuance (for example, your CDN renews and deploys certs), change alerts can drastically reduce time to detect when the wrong cert or chain lands on an endpoint.
Pros
- Purpose-built for certificate monitoring, not general uptime
- Change monitoring is valuable in automated renewal environments
- Flexible notification channels (Slack/Teams/SMS/webhooks)
Cons
- Typically paired with an uptime/synthetic tool for full availability coverage
- Less suited as a single “all monitoring” platform
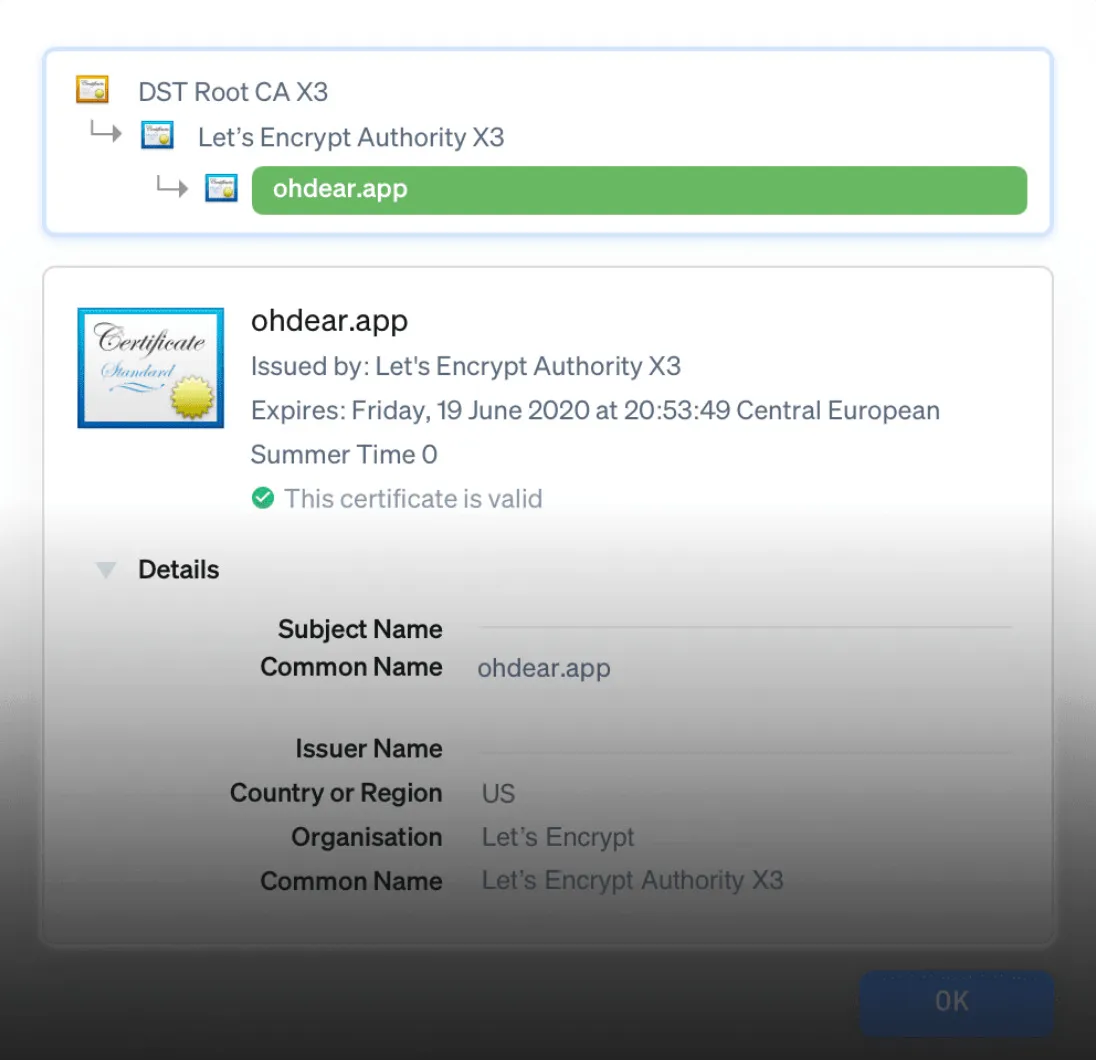
11. Oh Dear
Oh Dear’s SSL/TLS monitoring is built for teams that care about “did the certificate change?” as much as “is it expiring soon?” In addition to standard expiration tracking, Oh Dear highlights certificate change detection with a before/after comparison so you can quickly verify whether a renewal or deployment change is expected. This is particularly useful in 2026-era setups where certificates are rotated automatically by CDNs, reverse proxies, and managed platforms – because the failure mode isn’t always expiry; it’s the wrong certificate or chain being deployed somewhere in the path.
Operationally, Oh Dear fits well when you want monitoring that’s lightweight, readable, and integrated into developer workflows: strong notifications without turning SSL monitoring into a heavyweight governance project.
Pros
- Strong certificate change detection with clear before/after visibility
- Developer-friendly monitoring experience and notifications
- Useful for catching unexpected certificate swaps events in automated environments
Cons
- Not a full certificate management/governance system
- Best as an oversight layer alongside uptime/synthetic tools for availability context
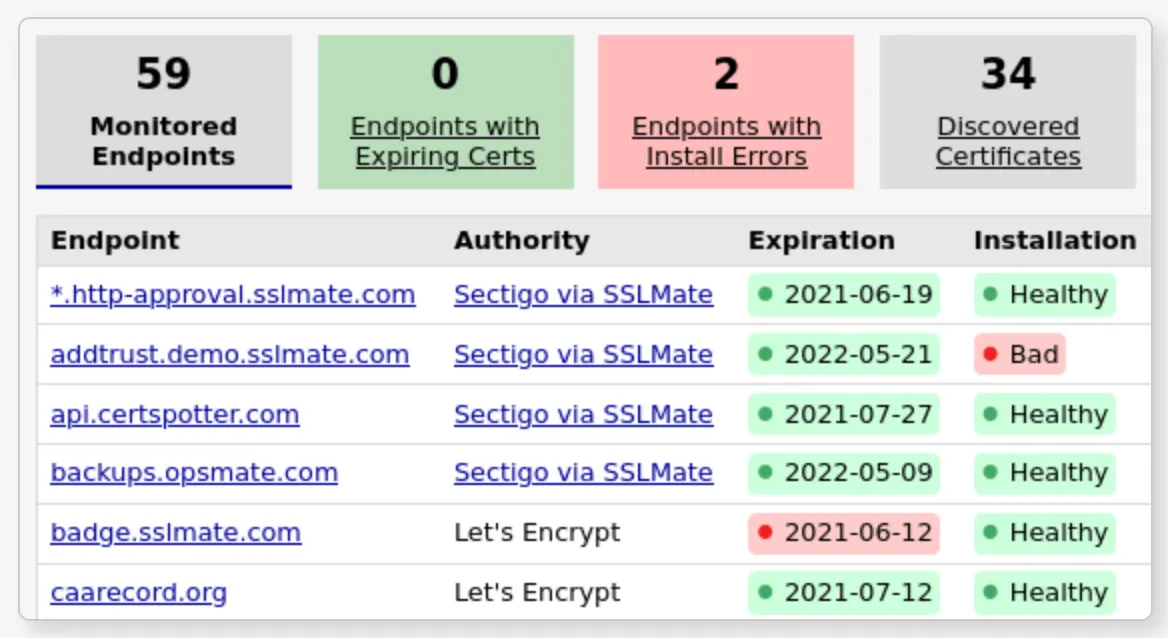
12. Cert Spotter (SSLMate)
Cert Spotter is a Certificate Transparency (CT) monitoring tool. Rather than only checking what your server currently serves, it watches CT logs and alerts you when certificates are issued for your domains – helping you detect unauthorized issuance, unexpected renewals, and certificate activity you didn’t plan. This is a different but increasingly valuable angle in 2026, because many organizations want independent visibility into issuance events, not just expiration reminders.
Cert Spotter exists both as a hosted service from SSLMate and as an open-source edition, which makes it appealing for security teams that want CT monitoring but prefer flexible deployment options.
Pros
- Excellent for detecting unauthorized or unexpected certificate issuance via CT logs
- Complements uptime/SSL-check tools by covering the “issuance event” layer
- Available as hosted service and open-source tooling
Cons
- CT monitoring is complementary, not a replacement for endpoint handshake/chain validation
- Less focused on uptime-style multi-location “what users see right now” checks
How to choose the right tool
If you want a practical decision rule:
- Choose a monitoring platform when you want SSL checks to be part of broader uptime and user-flow coverage, plus reporting and global checkpoints (for example, Dotcom-Monitor).
- Choose an incident-driven uptime tool when you want SSL failures to page like downtime (for example, Better Stack, Pingdom, UptimeRobot).
- Choose a synthetic-first tool when you care about chain issues and debugging context (for example, Sematext, Datadog).
Choose a certificate-focused tool when change detection and CT-style monitoring matters (for example, TrackSSL).
Conclusion
In 2026, the best SSL certificate monitoring tools aren’t just reminding you about expiry – they’re validating certificate health the way real users experience it and getting the right alert to the right team fast. If you want a solution that combines multi-location SSL validation, alerting, and reporting with broader website and transaction monitoring, Dotcom-Monitor is a strong place to start.