Organizations Worldwide
Platform Uptime SLA
Global Monitoring Locations
Website Monitoring Leader
What Is VPN Monitoring?
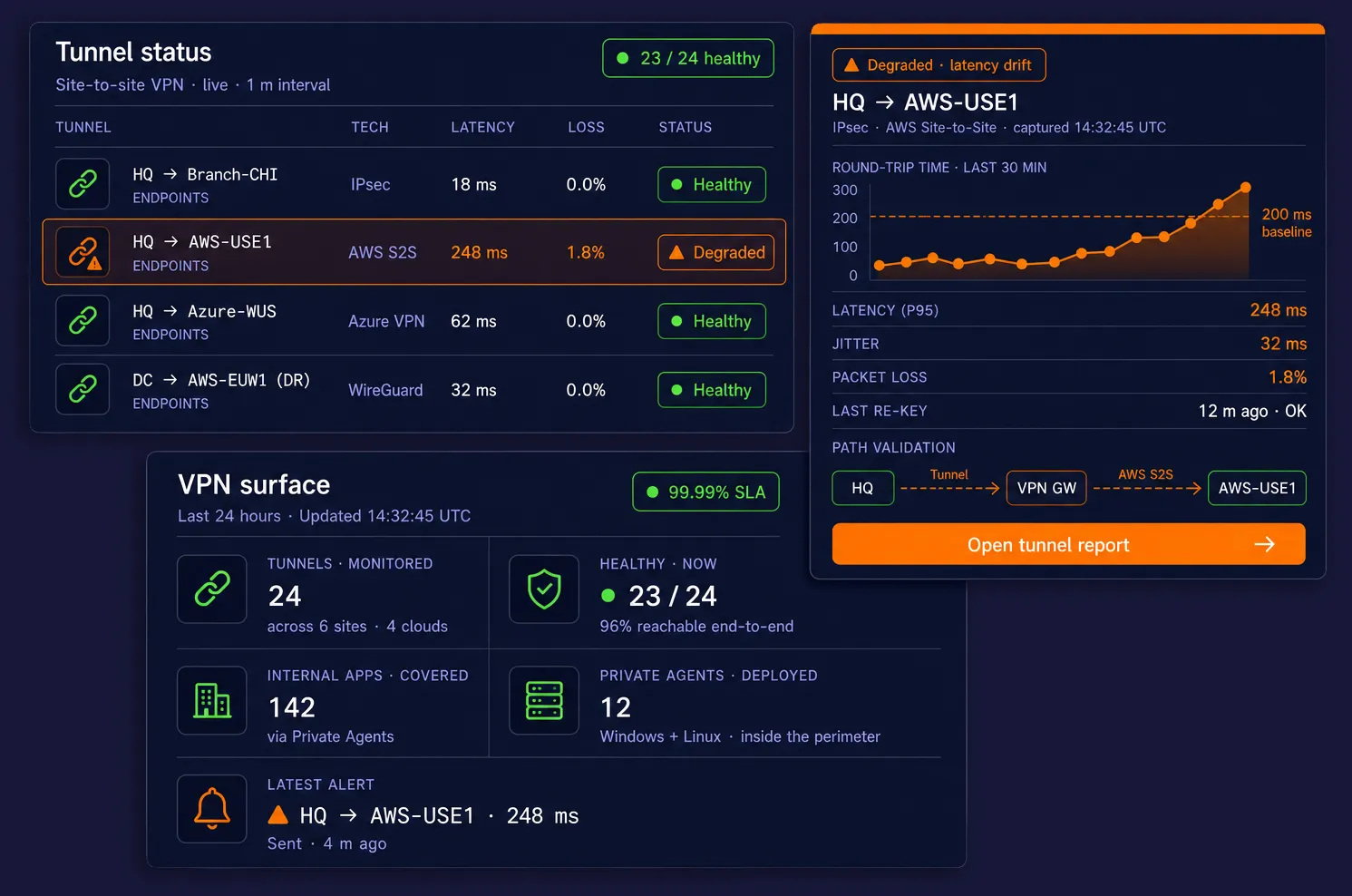
VPN monitoring is continuous, synthetic verification that your VPN-connected infrastructure is up, fast, and reachable — both the tunnels themselves and the services that live behind them. Dotcom-Monitor solves two distinct but related problems with the same platform: checking site-to-site VPN tunnel health between offices, data centers, and clouds, and validating applications protected by client VPN that external synthetic checks can’t reach.
VPN monitoring is the continuous, automated testing of VPN tunnels and the services that depend on them, so you can detect tunnel drops, latency drift, packet loss, certificate expiry, and application outages before users report them.
It covers two distinct patterns: (1) site-to-site VPN monitoring, which watches IPsec, GRE, DMVPN, WireGuard, or cloud VPN tunnels between offices, data centers, and VPCs; and (2) client VPN application monitoring, which synthetically tests internal web apps, APIs, intranets, and databases that are only reachable when a user is connected to the corporate VPN.
Dotcom-Monitor performs both from a single platform using Private Agents inside your network plus 30+ public monitoring locations worldwide, with 1-minute check frequency, ICMP/TCP/HTTPS/SNMP probes, and alerts over email, SMS, Slack, Teams, PagerDuty, and webhooks.