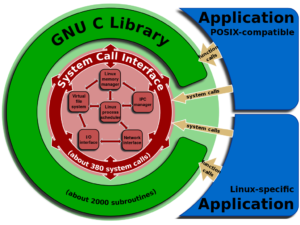
A DNS related exploit of Unix and Linux based operating systems has been gaining attention lately. The vulnerability exploits a bug in the GNU C library commonly referred to as the GLibC, serves as the core C library for many flavors of Linux and Unix based operating systems. This library is commonly used in linux based software including the DNS resolver. There are a number of manual fixes that can mitigate this GLibC DNS exploit but it is highly recommended that the glibc be patched immediately.
A previously known vulnerability in glibc has been found capable of exploiting a buffer overflow in order to attack and potentially gain control over a targeted machine. The vulnerability exploits oversized responses larger than 2048 bytes to overwrite the stack while using the functions send_dg over UDP and send_vc over TCP in getaddrinfo. Getaddrinfo is used in the DNS resolver indirectly in the DNS NSS module.
While no malicious exploits have been observed in the wild, the Google security team has proven a proof of concept that an attacker could exploit the bug if the attacker controls the domain name being looked up, the dns server resolving a name or by performing a man in the middle attack. They go on to specify that “Remote code execution is possible but not straightforward.” So essentially, a vulnerable Linux client machine that attempts to resolve a compromised domain could become infected due to this exploit.
How to mitigate the GLibC DNS Exploit
What should be done about it? As this GLibC DNS exploit is only known to affect Linux and Unix machines, make sure any Linux based machines you use are updated with the latest patches. Also, if you are concerned about your DNS records being hijacked to perform such an attack on your users, you might want to try out Dotcom-Monitor’s DNS monitoring service. You can enter your DNS server addresses, the host name to resolve and the expected answer. If the DNS server ever returns a different answer than expected you will receive alert notifications letting you know that something is not right. Sign up for a free trial to monitor your DNS record resolution today.